Internal Medicine is a broad medical specialty dedicated to the prevention, diagnosis, and treatment of diseases. Often referred to as the "queen of medicine," it offers a holistic approach by integrating a comprehensive understanding of the body's internal systems, ensuring that all aspects of a patient's health are considered.
Queen of medicine, doesn't that sound splendid. I guess that literally makes Dr. Gregory House the king of medicine. Being totally inspired on doing this blog post by re-watching House for 10th-ish something time, it struck me - information security is not so different from internal medicine, in fact, that is the closest profession I came up with - trying to do side by side comparison.
Surgeon cuts, orthopedist cracks, anesthesiologist blocks and internist rocks!
Internists know human body by hearth (you see what i did there?). Not only that (knowing human body by hearth - by any means should never be considered as "only"), they also have to know all sorts of things about environments, biology, chemistry and what not - medically and non-medically relevant.
Environments are changing, breakthroughs happen, diseases mutate, human bodies evolve and humans lie all the time.
As an internist, you have to adapt and stay up to date on so many levels and topics - at much slower pace then the information security professionals do, IMHO.
Information security is the holistic protection of information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction through the coordinated application of policies, processes, technologies, and human practices, in order to ensure confidentiality, integrity, availability, authenticity and nonrepudiation of information assets.
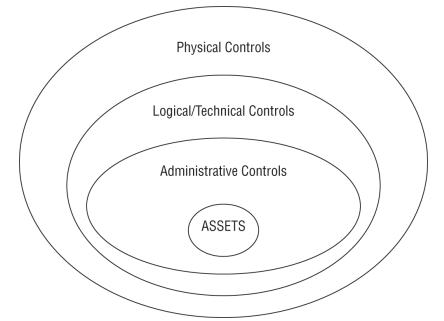
Look at all those layers, like an onion, doesn't that make you wanna cry? Well not if you - like me - are a sadistic nerd that enjoys burning his brains out.
We live in a digital era - duh. Most, if not all information - by now, is on digital media. Digital media is on computers, and a science that researches computers is called ...drumroll... computer science! - who would've told.
I am curious by nature, I love to know and I need to know hows and whys - I guess that is how it all started. I became an engineer, I love computers. To rest assure that asset is secure, that computer science thing is only the middle layer (logical/technical controls), and I won't even try drawing that onion, as it would turn out to be a 10kg cabbage on steroids - and a truck full of 'em.
Coders code, inventors invent, researchers research, designers design, administrators administer, and information security professionals ...are hated by most of 'em.
If you would to ask a web programming colleague - best in class - anything that deals with lower level or non-web programming and associated risks (use-after-free, oob writes, underflows/overflows), or not to mention non-programming related areas (IOT, OT, OS, RTOS, protocols, implementations, versions, standards...) he would've got no idea what am I talking about, and for a good cause, he simply - does not want or have to care - nor to know about its existence (sort of). Information security professionals on the other hand, have to.
Moore's law is the observation that the number of transistors in an integrated circuit doubles about every two years.
It is a bad practice saying that computers are evolving - it is not a evolution, it is a revolution, on a daily if not hourly basis - crazy!
A system is only as secure as its weakest link.
Remeber that 10kg cabbage? If one leaf is rotten, it is just matter of time when the whole thing goes bad.
We concluded that computers are revolving, thus policies, standards, procedures, laws and regulations need to follow. As much as internist does not have to be a chemist and information security professional also does not have to be a lawyer, they both need to have certain knowledge and presence in respective fields. I intentionally said certain - if you have less-er it makes you a lousy-er practitioner/professional.
Same thing with physical security, it is where all the fun begins - if you can't "touch" it, you can't break it. If there is no "exposure" of some sort you won't get sick. You gotta be aware of your environment, you don't have to be a military tacticians or an architect, but sure as hell you gotta lock and audit your data center.
Last but not least, everybody lies. Computers too. You have to stand your ground in front of executives, you gotta know your way around crowd, you gotta adapt your terminology to your audience, you gotta do your calculations right and efficiently manage your (mostly-non-existent) budget, you gotta do this, you gotta do that, blah, blah, blah, but you really gotta.
Next time you find out that a project manager (this is for the memes, i love all PMs I've ever worked with!) in your company - that excels at excel and word(s) (oah I did it again, you see?) and is a "peoples person" - is making double you do, remember that 10kg steroid cabbage I mentioned above, shove it in your executives face, share 'em this post and say 'em goodbyes.
I tried making this post as concise and short as it could be, considering we covered two wide-wide areas. Hope you had a great read, and you want to make an aspiring information security professional - or an internist!
As always,
Stay healthy, stay safe!
Cheers,
bigfella